The internet of things (IoT) has grown to a point where the entire world has become familiar with both its good and bad elements. Welcome to the era of the Internet of Things (IoT), where digitally connected devices are encroaching on every aspect of our lives, including our homes, offices, cars and even our bodies. With the advent of IPv6 and the wide deployment of Wi-Fi networks, IoT is growing at a dangerously fast pace, and Nokia’s Bell Labs Consulting suggests that there will be 20 billion such “other” devices connected to the network by 2020, outnumbering “IT” devices by almost 3 to 1. The range of devices using the IoT will be far more varied than for the classic Internet. Even if older industrial machines and accessories cannot connect directly, they can be retrofitted with additional devices to talk to the world. Meanwhile, an increasingly large number of other devices are now being introduced with IoT connectivity already designed into them. From baby cams, fridges, and toasters to turbines, locomotives, and smart buildings, web connections and traffic are multiplying exponentially.
Vulnerabilities and Threats:
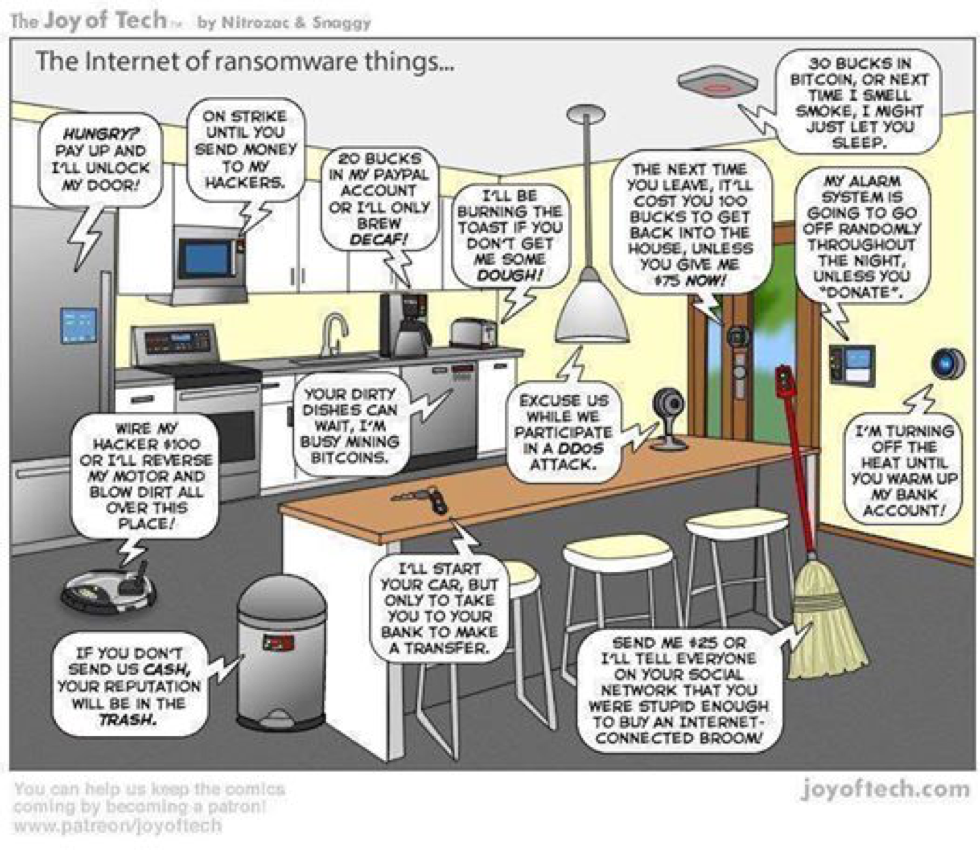
This exponential growth is not without risk. In the same way that security has become a critical issue for IT systems connected to the Internet, it is now having a profound impact on the IoT.
More connected devices mean more attack vectors and more possibilities for hackers to target us; unless we move fast to address this rising security concern, we’ll soon be facing an inevitable disaster.
The intelligence built into networked industrial machines and consumer electronics products makes them potential targets for cyberattacks. In many cases, such machines and products are programmed just once with few or even no updates afterwards. If a hacker infects these targets with malware or succeeds in taking control of them, the attack may remain undiscovered and untreated indefinitely.
Massive Opportunities for Cyberattacks
Now multiply this per-device risk by the number of possible targets, and it becomes clear how attackers could control armies of devices to spread further infection or generate massive amounts of traffic to bring legitimate systems to their knees (distributed denial of service or DDoS attacks). And multiply again by new Internet addressing schemes (IPv6) that increase available end-point addresses by orders of magnitude, and by the growing deployment by businesses of Wi-Fi networks feeding into the Internet, and the true size of the problem starts to become apparent.
Proven Vulnerabilities in Many IoT Devices
Even the innocent baby monitor connected to the IoT can in many cases be hacked to spy on live video feeds and remotely control the monitor. Cars connected to the Internet can be vulnerable too, as the ethical hacking of Jeep vehicles showed, allowing outsiders to take control of brakes, steering, and other crucial functions, all from a distance. Marketing pressure on device makers and their developers mean that products may be rushed through to release without proper security precautions or tests. A survey of product developers by security software vendor Auth0 showed that 90% of those developers thought that IoT devices did not have sufficient security in place.
Businesses Need an Effective Defense
Most businesses cannot influence the levels of security built into IoT devices – other than refusing to buy them or organizing a petition to stop their makers from supplying them. Many businesses find themselves at risk today because of the Wi-Fi network access they offer to their customers (guest Wi-Fi), which exposes them to the entire Internet and IoT. However, a business simply crossing its fingers and hoping that no army of IoT device “bots” will attack its network is not a realistic strategy. Even if IoT devices on the outside are potential or real threats, a business can now protect itself by adding effective, easy-to-manage security to its Wi-Fi network. This is especially important for smaller businesses that do not have the time or expertise to manage complex security solutions.
IoT Protection for Wi-Fi Networks from CaptiveXS
In addition to providing guest Wi-Fi features such as – Captive Portal, Content Filtering, Content Insertion; CaptiveXS has now incorporated the IoT security as part of its standard solution offering. New IoT discovery, management, and protection functions in the CaptiveXS solution from RaGaPa detect all devices (cameras, sensors, laptops, mobiles, tablets, consumer electricals, etc.) connected to a Wi-Fi network and categorizes them. Users can then associate different policies with these devices, ranging over quarantining, captive portal bypass, blocking, and capping of data throughput and bandwidth per device type. Out-of-the-box security ranks IoT devices as high, medium, or low risk, and bad devices can be automatically isolated or quarantined. Thanks to CaptiveXS, even though the world outside may be a dangerous place, businesses can at least protect themselves and their Wi-Fi networks from the inside.
